The purpose of developing a food fraud vulnerability assessment is for a food or beverage manufacturer/packer to ensure that control measures are put in place to prevent the receipt of materials that do not meet food safety and quality specifications. The intent is to gauge the business’ susceptibility to product substitution and adulteration as well as product mislabeling.
Step 1 – Gather information on raw materials and ingredients
The first step is for you to perform a literature search on your industry sector, ingredients/raw materials, and additives. Ingredients may be grouped based on product category, product formulation, provision by a domestic or foreign supplier or use by a specific manufacturing or packing site.
You may also consult the following sites to conduct your review:
- Trello (Free resource)
- USP (Paid service)
Using the USP database, we performed a search on 15 ingredients used in the formulation of typical gluten-free baked products.
Search results for the period 1980 to 2018 identified 21 food fraud records associated with 3 ingredients (tapioca, corn flour and sunflower oil). The other ingredients used in the recipe returned no hits. Among the fraud records, 8 were food-safety related. Adulterants included lime, melanine and ammelide. The USP database also provided a map (see below) with geographical locations of the publicized records. It also provided a list of detection methods, all of them well-known and validated.
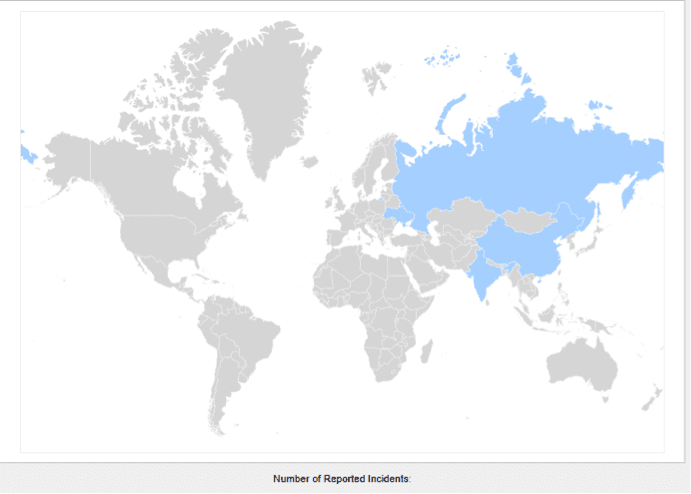
Blue countries are associated with reported food fraud incidents (Source: USP Food Fraud database search for “corn flour”, “tapioca starch” and “sunflower oil” – Total of 21 records for the 3 listed ingredients, 8 records are food-safety related).
Step 2 – Perform a risk assessment
You will first need to assess the likelihood of occurrence of the fraud. Criteria to consider include past incidents and emerging threats (import alerts, recall information, reports of outbreaks of foodborne diseases). Other factors may include the cost and seasonality of the ingredients or materials and the country of origin of the goods. The cost of adulterants and how easily the fraud can be committed could also be taken into consideration.
Best practices also require that you identify the likelihood of detection of committing the fraud. Considerations may include the physical form of the material and whether the product package is tamper-proof. Furthermore, are you able to determine if the fraud can be detected in the country of origin and early in the supply chain?
Based on our example and assuming the suppliers have yet to be approved, the risk assessment for materials purchased in North America or Europe would yield a “very unlikely” food fraud occurrence rating. Purchasing goods for countries that are known to be at risk would return an “unlikely” to “fairly likely” rating. The likelihood of detection would be very “likely/certain” (See the BRC white paper).
Step 3 – Determine the Food Fraud Vulnerability risk level using a risk assessment matrix
The risk matrix will return 3 risk levels for Food Fraud Vulnerability-based on the 2 criteria: “likelihood of occurrence” and “likelihood of adulterant detection”. (Refer to the BRC white paper).
High Risk
Materials and ingredients have been adulterated or substituted in the past. The risk is high and calls for rigorous controls. If control measures and verification protocols are not currently in place, your supplier approval program will need strengthening to ensure that safe materials are purchased from vendors that have a strong food safety culture.
Medium Risk
The raw materials and ingredients are at risk of fraud for economic gain. Control measures must specifically address all identified risks. Keep up-to-date on technological advances that may prevent food fraud in the future. Expect higher food safety practices from approved vendors (certifications, product testing).
Low Risk
Materials and ingredients are not likely to be adulterated. The plan needs reassessing if a product is re-formulated or materials purchased from new vendors.
Looking at our test product, the food fraud vulnerability would be low to medium risk. Nevertheless, considerations around the food safety status of the suppliers (compliance to food safety standards and regulatory requirements) would supplement the assessment and dictate the control measures to implement.
Step 4 – Establish controls based on the risk rating
Based on the outcome of the risk assessment, you will need to identify and implement controls to ensure the integrity and safety of incoming materials. Strategies may include:
- Shortening the supply chain by purchasing goods closer to the source, directly from the producer if possible.
- Building a strong supplier approval program which may include a need for suppliers to be certified or audited. This is critical for certain imported foods.
- Requesting a certificate of analysis with every batch received. Product may also be routinely sampled and tested upon receipt.
- Focusing on a smaller group of trusted and certified suppliers.
- Ensuring that suppliers maintain robust food safety programs. Sites with strong export policies, traceability and mass-balance programs are more likely to plan for potential issues.
- Verifying that suppliers are in good standing and compliant with import regulations.
Step 5 – Plan review
Your food fraud vulnerability plan must be reviewed when:
- New materials are acquired or are purchased from new suppliers.
- There is a change in the country of origin of the goods.
- The financial situation of the supplier or economy of the originating country may place the goods at risk.
- The value of the goods fluctuates, suggesting a potential adulteration of substitution.
- There are changes in the supply chain or the way materials are transported.
- Materials are scarce due to seasonal shortages.
- New risks emerge (import alerts, recalls, suppliers lose their food safety certification)
- New technological advances allow products to be routinely tested, thereby controlling the risk more effectively.
Sirocco can assist you with developing a food fraud vulnerability plan and food safety plan. Call us at 778.821.1392 today.
Reference: Understanding Vulnerability Assessment, BRC (2017)





